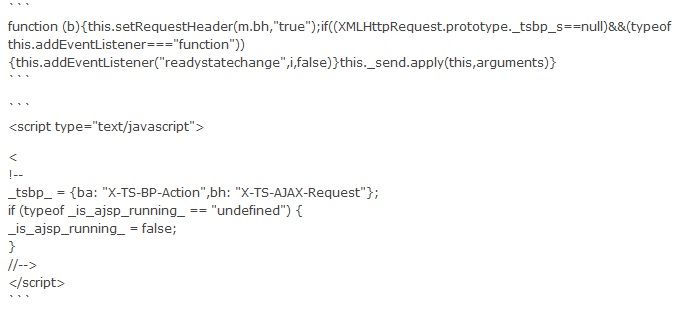
Do anyone know which feature in ASM module inject these scripts and how to change it ?
 Cirrus
Cirrus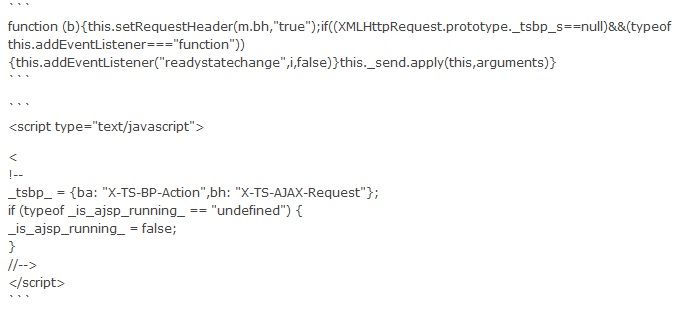
 Nimbostratus
NimbostratusFor anyone else who comes across this - it took me forever to find this settings because it's pretty buried. There's a few things in ASM that cause javascript injection:
It turns out that this is related to AJAX blocking, as I also had disabled the CSRF protection and I was still getting this injected into my pages, which was breaking a particular browser. When you first go to create your security policy, there's an option that you can check - AJAX blocking response behavior? This is going to inject that javascript in your pages.
In ASM 11.6.x, you can disable this setting by going to Security > Application Security > Blocking > Response Pages. Then you select the AJAX Response page from the tabs and uncheck the box.
Yes, this even injects the javascript if your policy is set to transparent mode! Yes, it's completely stupid!
Hope this helps, it caused me a ton of frustration.
 Nimbostratus
NimbostratusBy Doing this, Is there any impact on the application ? I think support ID will not be displayed in this case.