Automating ACMEv2 Certificate Management on BIG-IP
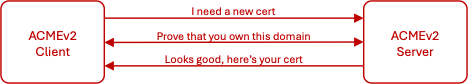
While we often associate and confuse Let's Encrypt with ACMEv2, the former is ultimately a consumer of the latter. The "Automated Certificate Management Environment" (ACME) protocol describes a system for automating the renewal of PKI certificates. The ACME protocol can be used with public services like Let's Encrypt, but also with internal certificate management services. In this article we explore the more generic support of ACME (version 2) on the F5 BIG-IP.346Views5likes2Commentsserverssl cipher suites
Hi, Is there an easier way to know what are the cipher suites that the backend server (pool member) can support? I have read an article but it requires to create a script. I know there is openssl but this will only show the cipher that the backend server used to communicate back with F5. So I was thinking like if from F5 perspective will it be able to perform an sslscan what are the available ciphers suites the backend server can support? Thanks, and regards, Rechie372Views0likes2CommentsMissing Certificate after redirect
We have a requirement for any calls coming into https://abc.comto be redirected to Azure APIM https://apim-xyz.com/api A simple following rule has been setup in F5 for calls coming intohttps://abc.com when HTTP_REQUEST { HTTP::respond 307 Location "https://apim-xyz.com/api" } But the problem we are facing is with client certificate. After the redirect, the client certificate is no longer available and new URL"https://apim-xyz.com/api"is not able to validate the request. We have no control over the client. We can control F5, redirect and server. Any help would be greatly appreciated.486Views0likes4CommentsTrouble applying GoDaddy certificate to a virtual server
I have created a few virtual servers and applied certs. They work just fine because they are using our internal CA. I have one now that uses a GoDaddy cert. I was provided a GoDaddy pfx file. I imported the cert and key without issues. I created the SSL profiles. In the CLientSSL profile, I chose the newly imported GoDaddy cert for Certificate, Key and Chain. I added the profile to the virtual server. When I open the virtual server in any browser, I get "The site can't be reached". Using FireFox, I get the error, "Error code: PR_CONNECT_RESET_ERROR". Because it's not an invalid cert error, I can't easily troubleshoot. Am I doing something that is glaringly wrong?Solved3.3KViews0likes18CommentsProvision IOS profile for Exchange ActiveSync with client certificate authentication
Problem this snippet solves: If you need to use client certificate authentication for ActiveSync services on IOS, you need to deploy custom profiles through a Mobile Device Management. MDM is maybe a little bit too much to achieve only this feature. The irule below provide necessary materials to provision a certificate and an exchange profile on IOS. Tested successfully on IOS 9. We use SCEP protocol for certificate enrollment. How to use this snippet: You need to define a Virtual Server and an access profile to publish ActiveSync. Then, you need to assign the irule on the Virtual Server. The certificate is retrieved using SCEP protocol on a Microsoft ADCS 2012 R2. The SCEP url should be changed in the Exchange payload. We configured APM to protect the access to this service and retrieve attributes from Active Directory but you can change the irule code to retrieve information and protect the service in a different manner. When a user reach /enroll uri with Safari browser, the provisioning process starts. /!\ I provide an IOS payload as example, but you need to modify it to fit your environment and save it as an ifile. Settings that need to be changed in the xml payload : <string>HOST.DOMAIN.COM</string> : Activesync FQDN <string>DOMAIN-Issuer-CA</string> : Issuing CA Name (if exists otherwise related code should be removed) <data>CERTIFICATE</data> : X.509 certificate in Base64 for Issuing CA <string>DOMAIN-Root-CA</string> : Root CA Name <data>CERTIFICATE</data> : X.509 certificate in Base64 for the Root CA <string>DOMAIN</string> : Organization name to be present in the user certificate <string>http://scep.domain.com/scep</string> : SCEP url External links Github : github.com/e-XpertSolutions/f5 Code : 68654 Tested this on version: 11.5764Views0likes1CommentAutomate import of SSL Certificate, Key & CRL from BIG-IP to BIG-IQ
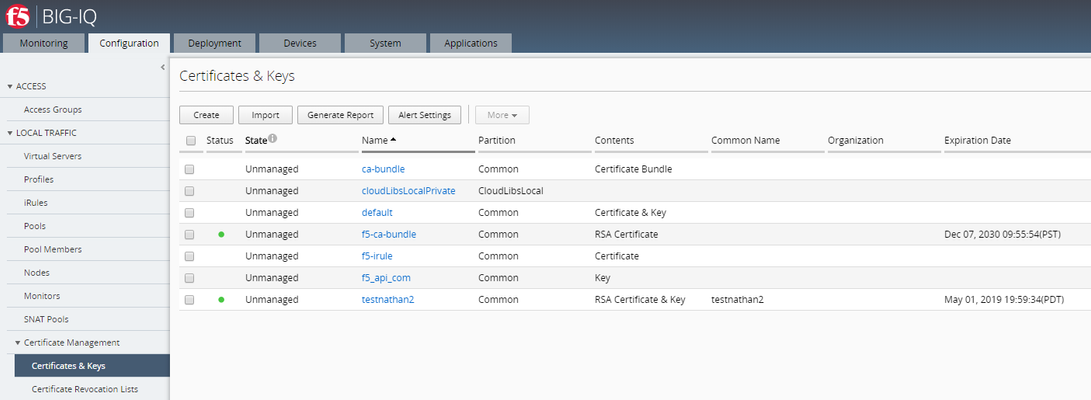
The functionality to automate the import of SSL cert & key from BIG-IP to BIG-IQ is available in the product starting BIG-IQ 7.0 and above. This script should not be used on BIG-IQ 7.0+ as it has not been tested on those versions. This script will import all supported SSL Certificate, Key & CRL that exist as unmanaged objects on this BIG-IQ which can be found on the target BIG-IP. Steps performed by the script: Gather certificateand key metadata (including cache-path) from BIG-IPs Download certificate and key file datafrom BIG-IPs Upload certificateand key file data to BIG-IQ Prerequisite:Discover and import LTM services before using this script.The target BIG-IP will be accessed over ssh using the BIG-IP root account. Installation:The script mustbe installed in BIG-IQ under /shared/scripts: # mkdir /shared/scripts# chmod +x /shared/scripts/import-bigip-cert-key-crl.py Command example: # ./import-bigip-cert-key-crl.py <big-ip IP address> Enter the root user's password if prompted. Allowed command line options:-h show this help message and exit-l LOG_FILE,log to the given file name--log-level {debug,info,warning,error,critical},set logging to the given level (default: info)-p PORT BIG-IPssh port (default: 22) Result:Configuration > Certificate Management > Certificates & Keys Before running the script: After running the script: Location of the scriptson GitHub:https://github.com/f5devcentral/f5-big-iq-pm-team In case you BIG-IQ is running on Hardware: Step 1: Install packages using pip, targeting a location of your choice # mkdir py-modules# pip install --target py-modules requests argparse Step 2: Run using python2.7, adding py-modules to the python path # PYTHONPATH=py-modules python2.7 import-bigip-cert-key-crl.py <big-ip IP address>4.9KViews1like43CommentsiQuery/ Big-IP DNS server certificate trust problem
Unable to establish iQuery between bigip devices. Connectivity is in place but failing with: SSL error:14090086:SSL routines:SSL3_GET_SERVER_CERTIFICATE:certificate verify failed I take this to be a certificate chain failure. The device certificates have been added to both DNS > GSLB > Servers > Trusted Server Certificates and System > Cert Mgmt > Device Cert Mgmt > Device Trust Certs. Yet, still no joy, running openssl confirms trust issues. Device certs are issued by a 2 tier PKI (intermediary and root). Big IP is 13 HF 2. Any suggestions? Is it common place to be using internal certs here?429Views0likes1CommentHow to Create a CSR in Powershell/iControl using an Existing Key
Hello, I am trying to automate CSR creation on the BigIP with iControl/Powershell. I can easily create new CSRs using new keys, but I can't figure out how to generate a CSR using an existing key. We need to do this so that we can update our SAN certs without invalidating the existing Certificate/key pair while we process the request with our provider. I use this to create a new key for a brand new CSR/Certificate request ... $CSRKey = New-Object -TypeName iControl.ManagementKeyCertificateKey_v2; $CSRKey.id = 'www.sitename.com'; $CSRKey.key_type = 'KTYPE_RSA_PUBLIC'; $CSRKey.bit_length = 2048; $CSRKey.security = 'STYPE_NORMAL'; ... but I can't find any functions in the iControl Reference Wiki to grab an existing key to use for the CSR. Can anyone point me in the right direction? Thanks!, Sean337Views0likes1CommentWindows 2012 CA certs for F5
Hi all, as we have to move our Certificates to SHA2 we have a new Windows 2012 CA server. After creating new Web certs from the new CA server, we had "Connection Closed" on different browsers when trying to reach the VIPs on port 443. The SSL client certs ciphers have been left as default. There's no irules and the VIPs are standard. When I put back the Windows 2003 CA certificates, it's working. I run the open ssl below and found that no certificates is shown with the new CA certs. I have compare both certificates and there's no difference in the properties that I can see other than the sha1 & sha2. Would anyone be able to advise what might be missing from our new CA server templates configuration ? [adm@Host:Active:Changes Pending] ~ openssl s_client -connect 172.20.50.20:443 CONNECTED(00000003) 47898972639784:error:140790E5:SSL routines:SSL23_WRITE:ssl handshake failure:s23_lib.c:184: --- no peer certificate available --- No client certificate CA names sent --- SSL handshake has read 0 bytes and written 277 bytes --- New, (NONE), Cipher is (NONE) Secure Renegotiation IS NOT supported Compression: NONE Expansion: NONE --- I check on both the certificate and key and there's are the same`` [adm@Host:Active:Changes Pending] certificate_d openssl x509 -noout -modulus -in /config/filestore/files_d/Common_d/certificate_d/:Common:Test.crt_77214_1 | openssl md5 (stdin)= 5773260e200ee58e7c89ae5a374d9a64 [adm@Host:Active:Changes Pending] certificate_key_d openssl rsa -noout -modulus -in /config/filestore/files_d/Common_d/certificate_key_d/:Common:Test.key_77211_1 | openssl md5 (stdin)= 5773260e200ee58e7c89ae5a374d9a64208Views0likes0Comments