ltm policy asm_auto_l7_policy
Hi Experts, We are migrating WAF in an HA pair from i4800 to i5800, UCS is loaded successfully on new pair. while comparing the configurations i found on some policy on previous node the status was legacy and on new node the status is published. what's the difference please? the status is highlighted in red in below config. old node config ltm policy asm_auto_l7_policy__epsite.telenorbank.pk { controls { asm } last-modified 2023-12-08:23:19:30 requires { http } rules { default { actions { 1 { asm enable policy /Common/PTCL-cloud_WAF } } ordinal 1 } } status legacy strategy first-match7 } New Node config ltm policy asm_auto_l7_policy__epsite.telenorbank.pk { controls { asm } last-modified 2024-04-17:13:00:12 requires { http } rules { default { actions { 1 { asm enable policy /Common/PTCL-cloud_WAF } } ordinal 1 } } status published strategy first-match }9Views0likes0Commentsxff and geolocation
If I want to create a dos l7 profile that needs to check the xff header as the source address (I will add an http+xff profile), and I want to exclude a country from the dosL7 policy using an LTM policy - can this be done with XFF? can the ltm policy recognise xff addresses' geolocations? If not with ltm policy, can this be done with an irule? thanks, Vered53Views0likes4CommentsiRule to Rewrite User Agent Header
We have a client that has an internal browser policy for IE to run in compatibility mode due to legacy applications. Unfortunately with the latest update to our application servers this causes issues with the content displaying properly. The application displays fine when the User Agent appears as one that is compatible. I have an iRule that I believe will work in concept; however I'm getting errors (See Below). when HTTP_REQUEST { Rewrite the User-Agent header value to show up supported browser if { [string toupper [HTTP::header User-Agent]] contains “MSIE 6” or “MSIE 7” or “MSIE 8” or “MSIE 9” or “MSIE 10”)}{ Replace the User-Agent header with supported user agent HTTP::header replace “User-Agent” "Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; rv:11.0) like Gecko" } } 01070151:3: Rule [/Common/HTTP-UserAgentHeader-Rewrite-iRule] error: /Common/HTTP-UserAgentHeader-Rewrite-iRule:3: error: [parse error: PARSE syntax 156 {syntax error in expression " [string toupper [HTTP::header User-Agent]] contains “...": unexpected operator &}][{ [string toupper [HTTP::header User-Agent]] contains “MSIE 6” or “MSIE 7” or “MSIE 8” or “MSIE 9” or “MSIE 10”)}] /Common/HTTP-UserAgentHeader-Rewrite-iRule:5: error: [undefined procedure: User-Agent&8221][User-Agent”] /Common/HTTP-UserAgentHeader-Rewrite-iRule:5: error: [undefined procedure: Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; rv:11.0) like Gecko]["Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; rv:11.0) like Gecko"]875Views0likes5CommentsHTTP Security Headers - LTM Policies
Hi folks, I'm trying to create some LTM Policies for the following: •X-XSS-Protection •X-Content-Type-Options •Content-Security-Policy •Strict-Transport-Security I already have the following working iRules, but would like to use Policies instead to limit impact on CPU: X-XSS-Protection when HTTP_RESPONSE { if { !([ HTTP::header exists "X-XSS-Protection" ])} { HTTP::header insert "X-XSS-Protection" "1; mode=block" } } X-Content-Type-Options when HTTP_RESPONSE { if { !([ HTTP::header exists "X-Content-Type-Options" ])} { HTTP::header insert "X-Content-Type-Options" "'nosniff'" } } Content-Security-Policy when HTTP_RESPONSE { if { !([ HTTP::header exists "content-security-policy " ])} { HTTP::header insert "content-security-policy" "default-src 'self';" } } Strict-Transport-Security when HTTP_RESPONSE { if { !([ HTTP::header exists "Strict-Transport-Security" ])} { HTTP::header insert "Strict-Transport-Security" "max-age=16070400" } } ...and here's what I've come up with so far for LTM Policy versions. Full disclosure, I'm a total novice with policies. Am I even close? ltm policy X-XSS-Protection { last-modified 2017-11-28:13:37:23 requires { http } rules { X-XSS-Protection { actions { 0 { http-header response insert name X-XSS-Protection value "1; mode=block" } } conditions { 0 { http-header response name X-XSS-Protection contains values { X-XSS-Protection } } } } } status published strategy first-match } ltm policy X-Content-Type-Options { last-modified 2017-11-28:13:37:19 requires { http } rules { X-Content-Type-Options { actions { 0 { http-header response insert name X-Content-Type-Options value "'nosniff'" } } conditions { 0 { http-header response name X-Content-Type-Options contains values { X-Content-Type-Options } } } } } status published strategy first-match } ltm policy content-security-policy { last-modified 2017-11-28:13:37:25 requires { http } rules { content-security-policy { actions { 0 { http-header response insert name content-security-policy value "default-src 'self';" } } conditions { 0 { http-header response name content-security-policy contains values { content-security-policy } } } } } status published strategy first-match } ltm policy Strict-Transport-Security { last-modified 2017-11-28:13:37:15 requires { http } rules { Strict-Transport-Security { actions { 0 { http-header response insert name Strict-Transport-Security value max-age=16070400 } } conditions { 0 { http-header response name Strict-Transport-Security contains values { Strict-Transport-Security } } } } } status published strategy first-match }1.3KViews1like5CommentsConvert language set iRule to LTM Policy
Hi folks, Hoping someone can offer some advice on converting an iRule to a LTM Policy. The rule is used to set a cookie which specifies either English or Spanish language on one of our websites. I have very limited experience writing iRules or Policies (the iRule in question was written by a consultant for us long ago). Below is the existing iRule: Determine whether to write the cookie when HTTP_REQUEST { Log our host and IP address log local0. "Host = [HTTP::host]; Client = [IP::client_addr]" Set our values based on host name, then by cookie's existence + value if { [HTTP::host] contains "es.test.company.com" } { Does cookie exist? Is its value 'es'? if { ([HTTP::cookie exists "i18next"]) && ([HTTP::cookie value i18next] equals "es") } { log local0. "Cookie exists and is set properly to 'en'" set write_cookie "0" } else { log local0. "Cookie will be written as 'es'" Flag to write a cookie set write_cookie "1" set value "es" } } else { Does cookie exist? Is its value 'en'? if { ([HTTP::cookie exists "i18next"]) && ([HTTP::cookie value i18next] equals "en") } { log local0. "Cookie exists and is set properly to 'en' " set write_cookie "0" } else { log local0. "Cookie will be written as 'en'" Flag to write a cookie set write_cookie "1" set value "en" } } } Now we set/update the cookie when HTTP_RESPONSE { if { $write_cookie == "1" } { log local0. "Setting cookie to $value" HTTP::cookie insert name "i18next" value $value domain "company.com" path "/" HTTP::cookie secure i18next enable } } ...and here is what I've come up with so far for a LTM Policy (which isn't working): ltm policy es.test.company.com-locality { requires { http } rules { domain_es { actions { 0 { http-set-cookie response insert domain company.com name i18next path / value es } } conditions { 0 { http-host host values { es.test.company.com } } 1 { http-cookie name i18next not values { es } } } ordinal 2 } domain_es_i18next_es { conditions { 0 { http-host host values { es.test.company.com } } 1 { http-cookie name i18next values { es } } } ordinal 1 } en { actions { 0 { http-set-cookie response insert domain company.com name i18next path / value en } } conditions { 0 { http-host host not values { es.test.company.com } } 1 { http-cookie name i18next not contains values { en } } } ordinal 4 } i18next_en { conditions { 0 { http-host host not values { es.test.company.com } } 1 { http-cookie name i18next contains values { en } } } ordinal 3 } } strategy all-match } Thanks!594Views0likes1CommentExtract SAN from Client SSL Certificate & Insert into HTTP Header
Hi folks, I'm working with some co-workers to setup some Slack.com forwarding in our environment. Mutual TLS and the insertion of the SAN from the client certificate into a HTTP header is a requirement. Can anyone help me come up with an iRule or LTM Policy to extract the SAN/CN from the client SSl cert and insert it as a HTTP header? Here's some additional info from Slack: Configure your TLS-terminating server to request client certificates. Your server should accept client certificates issued byDigiCert SHA2 Secure Server CA, an intermediate CA underDigiCert Global Root CA. These CAs are included in many standard CA certificate bundles. 1- Extract either of the following fields in the certificate. Subject Alternative Name:DNS:platform-tls-client.slack.com. ByRFC 6125, this is the recommended field to extract. or Subject Common Name:platform-tls-client.slack.com. 2- Inject the extracted domain into a header, and forward the request to your application server. Here's an example header you might add to the request:X-Client-Certificate-SAN: platform-tls-client.slack.com. Whatever you choose to call your header, check to make sure this header hasn'talreadybeen added to the request. Your upstream application servermust knowthat the header was added by your TLS-terminating server as part of the Mutual TLS process.Solved2.1KViews1like8CommentsPolicy action getting overwrote by irule
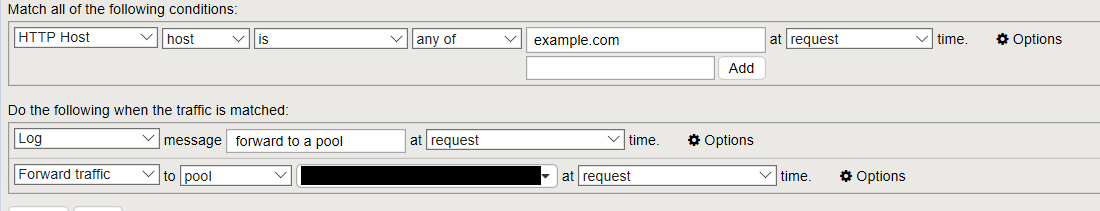
Hello Everyone, I'm currently using irule to publish application (filtering by URL). At the end of the irule I have a redirect by default. when HTTP_REQUEST {set path [string tolower [HTTP::path]] switch -glob [string tolower [HTTP::host]] { "example.com" { pool example-com-pool } default { HTTP::respond 301 Location "https://[HTTP::host][HTTP::uri]" } } I'm having an issue migrating from irule to ltm policies. I have this rule. My policy rule is matching (Thanks to the log action). But the forward traffic action is not working. I'm redirected to https by the default condition of the irule. So it looks like the irule is overwroting what my policy is doing. Anyone encountered this issue ? Thanks!Solved637Views0likes3CommentsLTM policy to redirect uri to correct pool
I am trying to create a policy which redirect the request to correct pool based on URI. So i am trying to use a simple logic i.e. If uri starts with /help or /assistance at request time forward the traffic to POOL A at request time. Rest all traffic should go to default pool POOL B. In the VS default pool is configured POOL B. But it is not working for some reason & default traffic is also hitting the POOL A resulting 404 sometimes vice versa. I also tried opposite mean if uri doesn't start with /help or /assistance redirect the traffic to POOL B at request time. Default pool in VS is POOL A. Still it is doing mix n match & creating 404 errors. Can you please help me to understand if i need to create the default rule under policy? I am unable to find a knowledge article which describes how to add default rule which redirects all the default traffic to default pool. So my policy looks like If uri starts_with /help or /assistance --> Forward traffic to POOL A Rest/default goes to POOL B Thanks!584Views0likes1CommentUsing LTM Policy to Redirect Host But Preserving Original URI
I am looking for some guidance and hopefully the community can help. We are trying to perform a host redirect using an LTM policy. The requirements are as follows: If URL contains uri /thisuri, forward request to pool http_server. If URL contains uri that is not /thisuri, redirect request to https://www.domain.com/[orginal_uri] We managed to configure our LTM policy to do everything except preserve the URI in the original request if URI is not /thisuri. Is preserving the URI from the original client request even possible when using an LTM policy? Has anyone tried doing something like this before? Our current logic is like this (we are using first match policy strategy): 1.test_uri_redirect Match all the following conditions HTTP URI > path > is > any of > /thisuri at request time. Do the following when the traffic is matched Forward Traffic > to pool > /Common/https_server > at request time. 2.test_host_redirect Match all the following conditions HTTP URI > path > is not > any of > /thisuri > at request time. Do the following when the traffic is matched Redirect > to location https://www.domain.com > at request time. All that we are missing is how to tell the BIG-IP to preserve the original URI path. Any help would be much appreciated.1.7KViews1like3Comments