Application Auto Scaling Through BIG-IP Cloud Edition
Peanut butter is good and jelly is good. What happens when you bring those two together? BIG-IQ 6 is the peanut butter, Per App VE is the jelly. Put them together and you get per application auto scaling. BIG-IP supported auto scaling for a while now but the use cases of dynamically deploying multiple instances of BIG-IP were few (based on individual application requirements). By deploying the BIG-IP Per App VE instead, you get a (marketing speak alert) lower cost deployment for customized ADC and security on a per application basis. Our training team put together a great walk-through article for deploying auto scaling features with BIG-IP Cloud Edition. In our two videos we'redeploying auto scaling functionalityinto VMWare and AWS infrastructures. For comparison go back and check out Skies Never looked So Good With BIG-IP Cloud Edition where we show the differences between AWS and VMWare tier 1 traffic distributors. But enough talk... Enjoy the walk-through. A discussion in Q&A for BIG-IP Cloud Edition is available if you have questions. Further Reading ASKF5 BIG-IP Cloud Edition Knowledge Center BIG-IP Cloud Edition - Deploy and Secure an Application BIG-IP Cloud Edition & Per App VE FAQ Getting In Shape For Summer With BIG-IP Per App Virtual Edition ASKF5K33431282: Overview of BIG-IP Cloud Edition Components829Views0likes0CommentsBuilding Applications For The Rest Of Us With BIG-IQ 6
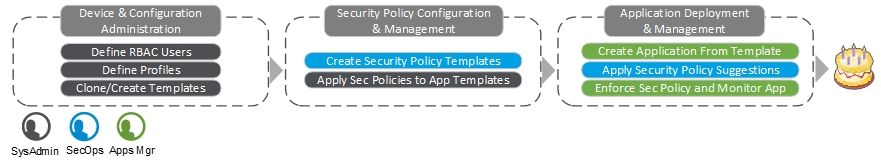
If you enjoy hoarding vast depths of knowledge from your business partners this article is not for you. If you want to provide a scalable and simplified deployment model to empower and enable your teams then read on my friend. Of of the two pieces of the BIG-IP Cloud Edition ecosystem, BIG-IQ 6.0 provides a streamlined way to deploy applications for the rest of us. Tying simplified application deployment to BIG-IP Per App Virtual Edition's auto-scaling functionality within AWS or VMWare, Cloud Edition provides scalable deployment models you've been looking for from F5. Quick application compliance is a button click away for any team wanting complete ADC and Advanced WAF features provided by BIG-IQ and BIG-IP. Using role-based access controls (RBAC) our below example will deploy an application with the assistance of a BIG-IP admin, a Security Manager, and Application Owner. A Template for You and A Template For You; Templates for Everyone! Our BIG-IP admin provides a service catalog of application templates to users who have roles allowing app creation/deployment. Predefining a service catalog gives them the ability to create traffic profiles and tune networking requirements without complicating the deployment process for his application owners. This keeps our BIG-IP admin in control of the network and applications traffic profiles running on it without slowing down deployments. In our example, they'llclone a BIG-IQ default template so the rest of the team can deploy a web application firewall (WAF) enabled application. Our security engineer will create his security policies based on corporate compliance requirements and Dwayne will apply Mick's security policies to the service catalog offerings. Mary our App Manager will choose the new WAF enabled catalog item to deploy a new application in front of her web servers. tl;dr - check out the pretty picture. BIG-IQ 6 comes with several prebuilt templates. They're quite useful for new BIG-IQ administrators to review so they'll see how service catalog items are built from preexisting BIG-IP profiles and configurations. The prebuilt templates, similar to default BIG-IP profiles, are not modified by administrators but cloned or used as references for new service catalog offerings. Note: Templates that do not define an HTTP profile cannot be deployed to a service-scaling group (used for auto-scaling in AWS and VMWare). Security Policies Our Security Manager needs to build a new WAF template for the upcoming application. They've been granted the Security Manger role within BIG-IQto create and manage security policies, relying on the BIG-IP admin to apply them to service catalog items. In this particular case our Security Managerwill edit the policy viol_subviol, change the learning mode to manual and make it available to application templates for use. To apply the new security policy, the BIG-IPadmin will clone the default f5-HTTPS-WAF-lb-template, in this case we're calling it f5-HTTPS-WAF-lb-custom1 (not too creative, I know). The admin can now select theupdated ASM policy viol_subviol and the logging profile templates-default for the virtual servers. Deploying A Service Catalog As An Applications With our creation complete our Application Owner can log into BIG-IQ and starting deploying. TheApplication Manager role wasgranted and will permit them to deploy, edit, and monitor applications (within allowances set by our admins service catalog template). When our App Manager logs in, they'll see a Application Manager specific dashboard; RBAC limits the Application Manager role's view and prevents access to device, security, or global configurations. They'llcreate a new application named site18.example.com (she's not very creative either) based on our predefined f5-HTTPS-WAF-lb-custom1 template. The only information our Application Managerneeds to provide tothe service catalog is the IP address of the virtual server, the IP address and ports open for the application servers, and the FQDN of her application. The Application Managerfills out the application template and clicks Create. BIG-IQ is off to the races to deploy the application and within minutes we'll sees a healthy status on the new site18.example.com application. NOTE: If there was a configuration issue or deployment failure, Dwayne our admin can tail the BIG-IQ logs at /var/log/restjavad.0.log to determine the cause. If the Applicaiton Managernoticed an issue they can click through the application dashboard to find out further details. In this case, the application is fine but they'll update the application health alert rules to coincide with the application's SLA. We can also request other people in the applicaitonteamaccess to monitor this application specifically without viewing others. Our BIG-IP adminhas no problem achieving this with RBAC. Reviewing Application Statistics Application deployment is complete and the Appteam has completed traffic and application testing. Our security manager will log back in, check the viol_subviol ASM policy and then accept the learning completed from thetesting. After that they'll change the enforcement mode to blocking. When our Application Managerlogs back in they can click on security within traffic diagram under Application Services. This will give them security specific analytics and configurations. "Start Blocking" is available for our managerto enable now now that traffic learning was accepted and applied to the system. Sooner or later some cranky people start sending us some malicious traffic some malice and we can view the changes in traffic behavior. Automating Your Deployments BIG-IQ can also assist with automation. BIG-IQ's use of RBAC allows administrators to create automation-centric service accounts for deployment and management needs. Administratorscan segregate service accounts based on unique requirements and further control your application lifecycles as you and your team see fit. ShouldApplication Manager have decided to deploy the application via Ansible they could have clicked View Sample API Request and BIG-IQ will provide the JSON snippet along with entered data to populate the playbook. Of course this is a one-off example but it's providing the template needed to deploy further applications should Ansible authenticate with the appropriate credentials. BIG-IQ 6is a significant step forward to provide ADC and Security functions in front of ALL of your applications, not just the mission critical. We just scratched the surface with application deployment in what BIG-IQ 6 can do for you. In our next article we'll cover auto-scaling applications using service scaling groups with BIG-IP Per App VE. Together BIG-IQ and Per App VE form BIG-IP Cloud Edition and a new way to protect and maintain all of your applications no matter how big or small. As always, if you have questions or feedback, please go to our BIG-IP Cloud Edition Discussion in Q&A. Happy Admining.731Views0likes4CommentsGetting In Shape For Summer With BIG-IP Per App Virtual Edition
What happens when you cross a developer with a fitness instructor? I can't think of a punch line that won't make you hate me. But there's really no joke here. Last January F5 released a new version of BIG-IP and something interesting was lurking under the hood of those extra decimal places. Similar to my discussion of BIG-IP's SELinux updatesthese features don't always get noticed but it's important for you to know when making deployment decisions. Grab your protein shake and let's see what changed so far. Dropping The Weight It's a universal fact that Storage Admins eat their young so the last thing you want to do is ask for excessive amounts of disk space. Our developers took that to heart and trimmed down BIG-IP virtual edition to nearly half of it's predecessor. Don't believe me? Here is a side by side of a vanilla BIG-IP EC2 instance in AWS. Here's BIG-IP v12 after a nice holiday season of figgy pudding and candied yams. BIG-IP v13.1.0.2kept their New Year's resolution intact and shed those gigs! How many BIG-IP virtual editions do you really have deployed, is the storage savings worth it? Some of you can count on one hand, some of you need your hands and toes... or your coworkers hands and toes too. If I deploy 5 BIG-IP v13.1.0.2 (or later)instances I'll save roughly 240GB of storage compared to earlier versions. What if I deployed 25? Over 1TB of storage saved but who's deploying 25 BIG-IP's at a time? Hold that thought. Usain Bolt Has Nothing On Our Deploy Time Cloud deployments expect application availability in minutes not hours. F5's developersarealways looking for more ways to speed up time between pressing the deployment button and actually passing traffic between clients and applications. An internal team didexactly that and here are some results of our initial tests in AWS. Mind you these numbers will always fluctuate depending on how complexyour automation is and how complicated you like to make your configurations. Notes on cloud testing in AWS: Region: Canada Size: m4.xlarge - 4vcpu/16GB RAM Disk: io1/gp2 Image Size: Good 41G And from what I've seen, these numbers are only getting better. We have a faster deploymet times to processing traffic after initial deployment. Now what? Hold thatthought too. Per App VE - Where The Work Pays Off Public or private cloud, administrators still deploy BIG-IP virtual edition similar to how they deploy BIG-IP hardware. A monolithic device providing reliable application delivery controller and security services supporting hundreds or thousands of applications. This is still a popular method to install BIG-IP in traditional or hybrid data centers. Developers can still programmatically configure monolithic BIG-IP virtual instances; application services spin up and down while updating nodes and configurations to BIG-IP via our REST interface. However you'll always have applications who may not have access to the "corporate" BIG-IP infrastructure or an application owner may need a unique instance to test a CI/CD process and they're segregated away productioninfrastructure. Or your teams just like their own application sandboxes. Enter BIG-IP Per App Virtual Edition (VE). BIG-IP Per App VE is a bandwidth and CPU licensed offering that createsa reduced cost solution designed to provide Local Traffic Manager (LTM) and Web Application Firewall (WAF) features programmatically on a per-app need. Combined with BIG-IQ as a full management solution for orchestration management or just using the BIG-IQ License Manager (free) you can deploy BIG-IP wherever developers and application teams need. BIG-IQ is NOT needed to purchase BIG-IP Per App VE but it makes licensing a lot of deviceseasier. What does the license provide and how do you provision? I'm glad you asked. The BIG-IP Per App VE License: 1 virtual IP address 3 virtual servers or 1 (a combination of virtual address and a listening port) 25 Mbps or 200 Mbps throughput (license dependent) LTM or LTM with Advanced WAF 1 Interface BIG-IP Per App VE Instance Requirements Minimum Maximum vCPU 2 4 Memory 4 16 Disk 40 82 Remember you were holding two thoughts? The post-diet VE image available in v13.1.0.2 or later and the improved boot times? Suddenly this should start coming together for you. You can now deploy a realistically sized full featured security and ADC solution whodeploys and processes traffic when your application needs it to and costs a lot less than the traditional "monolithic BIG-IP". Developers can now get work with BIG-IP LTM and Advanced WAF services where they need them insted of being forced to subscribe to the stricter management that come with larger consolidated deployments. Where are we going? The BIG-IP Per App VE is that first step to providing a more robustsolution into continuous delivery/integration platforms and puts security and adc features closer to the developer and applicaiton owners. It's hard to require developers to adopt a security position when traditional infrastructure createroadblocks (ITIL, I'm looking at you). You'll still need those restricted systems for mission critical applicaitons where downtime breaks SLA's and contractural agreements. For all of those high priority applications BIG-IP Per App VE is your answer. F5 is busily working on building on the flexibility of the Per App VE license into emerging products to make deployments and scalability a piece of cake. So I'll ask you to again... hold that thought. ; )570Views0likes0Comments