API feed for WAF Attack Signatures
Hi again! This is my 3rd question post today and I'll try to make it my last for today. 😄 I'm a project manager responsible for our WAF implementation and I'm more involved in WAF care and feeding than a project manager should be. Is there an API feed available for WAF attack signatures both current and staged? Our WAF logs are fed into Splunk and Oracle. In Splunk, I built an Excel spreadsheet that I use as a lookup table that has current and staged attack signatures. I had help pulling the JSON feed from the F5 attack signatures database. I have to manually add to this file as I suspect our logging activity is causing additional characters such as percent signs to show up in the sig_ids field for my Splunk reports. As mentioned in one of my other posts, my manager wants to move over to an Apex application that one of the application developers on our WAF team has been building. The goal is to allow our business owners to authenticate and view WAF related reports that we develop for their organization. If we move to Apex, this renders the Splunk lookup table I've built and maintain useless, thus, I'm on a hunt for an API. If anyone has suggestions for staged attack signature management, I'll take those as well. I was told that I should monitor them which I am but our tuning and remediation processes are so tedious that I'm not sure how to work in yet another meeting to review and discuss staged attack signatures. 😒 Thank you! Jodi5Views0likes0CommentsWAF Organizational Processes
Hello! I'm a project manager responsible for our WAF implementation and likely more engaged in WAF care and feeding that most project managers. 😀 I'd like to understand from others their WAF organizational processes with the goal of improving ours. I'm responsible for hosting a weekly WAF tuning meeting. Our WAF admin pulls data from our Splunk logs and brings up samples for policies that we've not yet put into production mode. Our WAF admin wants our two application developers on our WAF team to say "yea" or "nay" for each sample to be tuned. This is incredibly tedious but our hope is to reduce false positives. How do other orgs handle pre-production tuning? We have a similar process if a production deployed policy receives a block. Our business owner for the application opens a ticket for their end user. Since I'm not allowed access to F5 WAF, I use the support ID to look up the WAF report in an Apex application one of our developers wrote. I provide this report to our WAF admin who waits for one of our WAF team app devs to say "yea" or "nay" on whether it's legit traffic. If it's legit, he tunes the policy but sometimes still with apprehension. This results in either my needing to schedule a special meeting with our WAF team (includes me, 2 apps devs, WAF admin, sys admin manager, my manager, and 1-2 reps from security) or taking time in a tuning meeting to review the tuning adjustment that was made and get a ruling on whether it it's too risky to keep in place or it's safe to remain. How do your organizations handle reports of blocks from your business owners and their end users? I truly feel we can and should improve so I'm eager to hear what others in the community are doing. Thank you! Jodi6Views0likes0CommentsSMTPS relay to external MS 365
Hello, My organization has a requirement where internal application servers that send SMTP emails need to relay that traffic and secure the emails going outbound to MS365 servers. I have not discovered any specifics on Myf5 or via web searches. Can anyone point me in the right direction or if a solution exists, please send me a link to said solution. Thank you, et8Views0likes0CommentsSuspicious SSL TPS Spikes
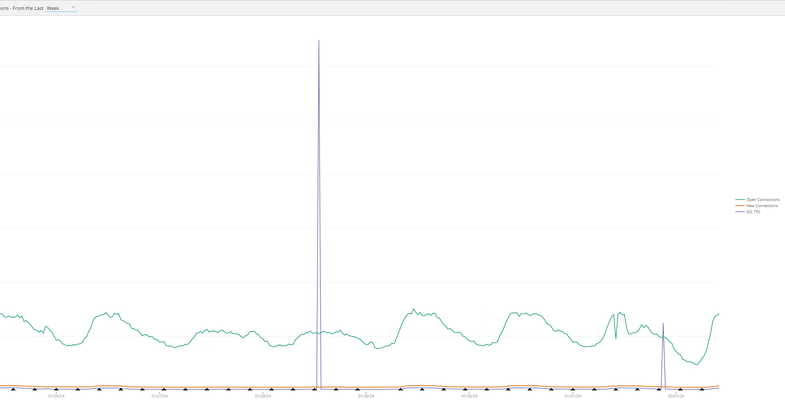
Hello, I'm kind of struggling to wrap my head around some weird spikes I'm seeing on the F5 BIG-IP Dashboard. We had two of these spikes this week, hitting like x1200 more SSL TPS than our usual high average. I'm thinking it might be some kind of attack, given the fact that we also faced some DDoS recently, but honestly, I have no clue how to dig deeper into it. Or is it possible to be a bug (found this: https://cdn.f5.com/product/bugtracker/ID499348.html) ? Any ideas are highly appreciated, thank you!62Views0likes0CommentsCybersecurity Awareness Month - Fun with Passwords
Head over to the password game and let me know what level you check out at! And Happy Cybersecurity Awareness Month! What security technology are you learning this month? Can't seem to embed shorts here...but here's my attempt: https://youtube.com/shorts/3dtrcAmi__E?si=6dVwa8iKI3IPH8wh607Views5likes3CommentsAsking for advice on a career in cybersecurity
Hi F5ers, I hope you are doing well. After getting F5 401 and 402 certified, and working with many security solutions during the last 13 years, I am planning to go deeper into other cybersecurity fields, like security auditing, governance and compliance, risk management... If anyone has already taken a similar move or has experience with other cybersecurity fields, please share what would be a good track for learning and certifications. Any information or advice is welcome Cheers1.2KViews3likes3Comments